The brute-force approach is the most time-consuming password recovery method. We are proud to share that we have introduced Mask attack that significantly reduces the time spent on password recovery by skipping unnecessary character combinations.
The new version of Passware Kit also supports the latest version of iWork, accelerates Windows user password recovery on GPU, recovers passwords for 7-Zip archives on Linux and Mac, and improves performance for Zip AES files by 40%.
What’s new in Passware Kit 2020 v4
- New Mask attack
- Password recovery for iWork 2020 files
- New modifier: English – Arabic keyboard layout transliteration
- GPU acceleration for NTLM hashes
- Improved performance for Zip AES password recovery
- Password recovery for 7-Zip archives on Linux and Mac
- Reports saved as CSV files
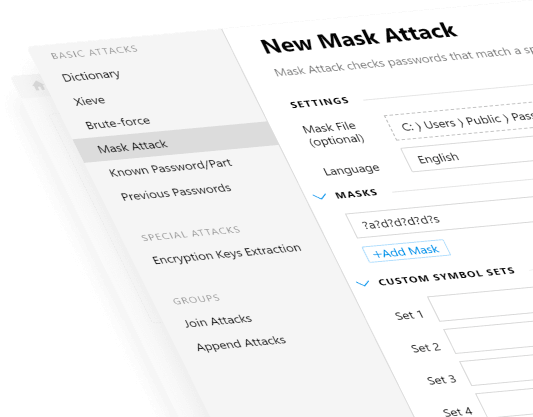
New Mask attack
Passware adds a new password recovery method: Mask attack that checks passwords matching a specific pattern. A password mask is a string that displays a position of character candidates in a password.
The new attack allows users to skip unnecessary character combinations and reduces time spent on brute-force password recovery.
The Mask attack is compatible with hashcat mask files (.hcmask).
Password recovery for iWork 2020 files
Passware Kit recovers passwords for iWork files: documents created with Pages, Numbers, and Keynote. The new version introduces GPU-accelerated password recovery for the latest iWork 10.2.
New modifier: English – Arabic keyboard layout transliteration
The new version of Passware Kit adds support for English <-> Arabic keyboard layout transliteration to the Substitute Characters modifier, which is applicable to all types of brute-force attacks: Dictionary, Xieve, Brute-force, Previous Passwords, etc.
This makes it possible to recover passwords when an English word is typed in the Arabic keyboard layout and vice versa.
GPU acceleration for NTLM hashes
Passware Kit now accelerates the recovery of Windows user passwords from NTLM hashes. It features a GPU acceleration on both NVIDIA and AMD cards, providing the average speed of 19 billion (!) passwords per second on an NVIDIA 2080Ti.
Decryptum DPR 2080TI-S/12 4U provides the speed of up to 180 billion passwords per second.
Improved performance for Zip AES password recovery
GPU acceleration of password recovery for Zip archives is even greater now! Passware Kit 2020 v4 recovers Zip AES passwords 40% faster, reaching the speed of 6 million passwords per second on an NVIDIA 2080ti GPU.
Decryptum DPR 2080TI-S/12 4U is now over 280% faster, processing up to 40 million Zip AES passwords per second.
- Decryptum
- Passware Kit Forensic
- Passware Kit Business
- Passware Kit Standard Plus
- Passware Kit Standard
Password recovery for 7-Zip archives on Linux and Mac
Passware Kit Agent for Linux and Passware Kit Forensic for Mac now support password recovery for 7-Zip archives, in addition to the Windows version of the Passware Kit.
Reports saved as CSV files
Passware Kit is now able to save password recovery reports as CSV files. This makes it easy to process decryption results using third-party tools.
CSV reports include the following information: file path, account name, and password.
Decryptum™ Password Recovery
In partnership with Comino, we have developed Decryptum – ultra-compact liquid-cooled GPU accelerated devices for password recovery and decryption. Decryptum PR 2080TI/12 4U is the ultimate scalable turn-key decryption solution: a single 4-unit system is powered by 12 x 2080TI GPUs and delivers unparalleled performance.

| File type | Passwords / second* |
|---|---|
| MS Office 2013+ | 285,000 |
| macOS / FileVault2 / APFS | 210,554 |
| RAR 5 | 1,205,000 |
| MS Windows / BitLocker | 40,000 |
| Zip AES | 39,000,000 |
* High-performance mode (overall performance may vary ±3%).



